前言
前后端分离的开发模式中,接口的认证与授权是重中之重。由于接口都是无状态的,那势必就需要一套认证和授权框架来解决“你是谁”以及“你能干什么”的问题,所以,这篇文章就来聊一聊如何整合SpringSecurity和JWT实现登录认证和授权。
源码传送门:https://gitee.com/huoqstudy/xiliu-admin.git
一、SpringSecurity是什么?
SpringSecurity是一个强大的可高度定制的认证和授权框架,对于Spring应用来说它是一套Web安全标准。SpringSecurity注重于为Java应用提供认证和授权功能,像所有的Spring项目一样,它对自定义需求具有强大的扩展性。
其核心就是一组过滤器链,在spring security中一种过滤器处理一种认证方式,项目启动后将会自动配置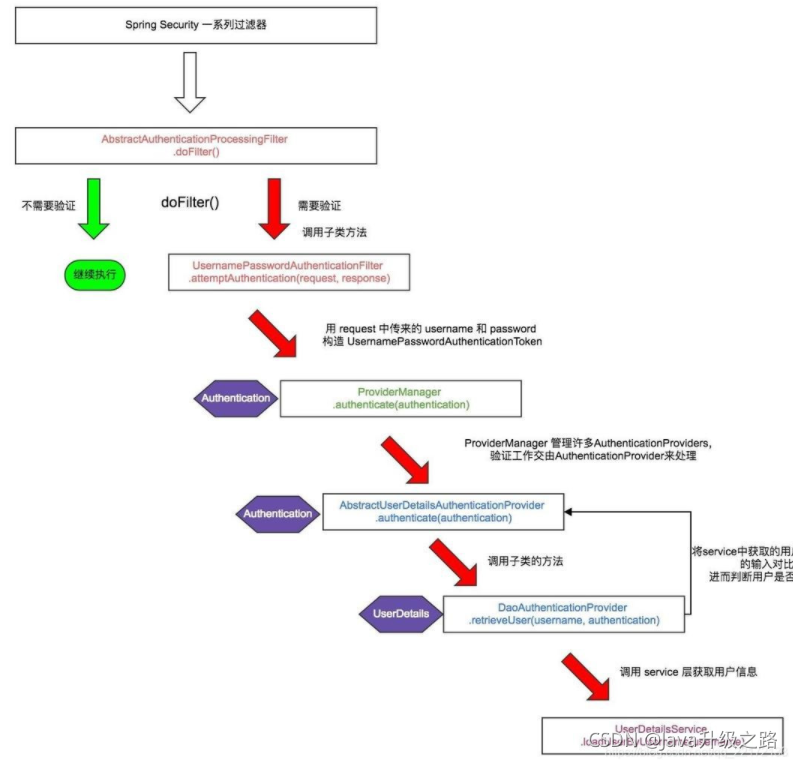
二、JWT是什么?
JWT是JSON WEB TOKEN的缩写,它是基于 RFC 7519 标准定义的一种可以安全传输的的JSON对象,由于使用了数字签名,所以是可信任和安全的。总结来说,JWT只是一个生成token的机制。
1. JWT的组成
JWT token的格式:header.payload.signature
可以在该网站上获得解析结果:https://jwt.io/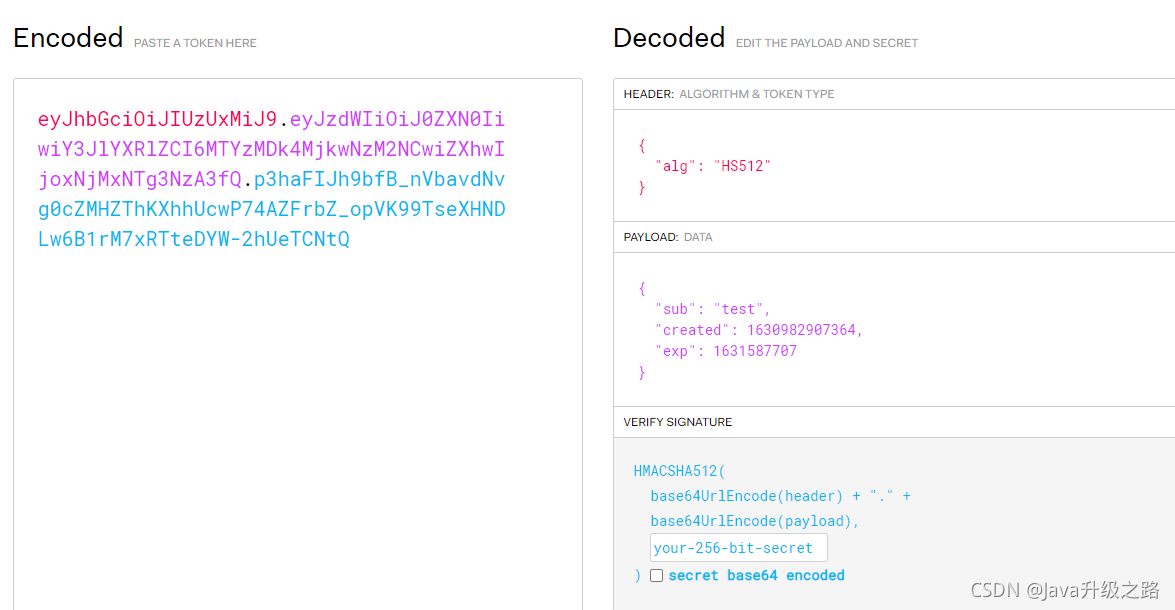
header中用于存放签名的生成算法
payload中用于存放用户名、token的生成时间和过期时间
signature为以header和payload生成的签名,一旦header和payload被篡改,验证将失败
2. JWT实现认证和授权的原理
- 用户调用登录接口,登录成功后获取到JWT的token;
- 之后用户每次调用接口都在http的header中添加一个叫Authorization的头,值为JWT的token;
- 后台程序通过对Authorization头中信息的解码及数字签名校验来获取其中的用户信息,从而实现认证和授权。
三、整合步骤
1. 引入相关依赖
代码如下:
<!--SpringSecurity依赖配置--><dependency><groupId>org.springframework.boot</groupId><artifactId>spring-boot-starter-security</artifactId></dependency><!--JWT(JsonWebToken)登录支持--><dependency><groupId>io.jsonwebtoken</groupId><artifactId>jjwt</artifactId><version>0.9.0</version></dependency>2. yml配置中加入jwt配置信息
jwt:
tokenHeader:X-Token #JWT存储的请求头
tokenHead:Bearer #令牌前缀
secret: yz-admin-secret #JWT加解密使用的密钥
expiration:604800 #JWT的超期限时间秒(60*60*24)3. 添加JWT token的工具类
用于生成和解析JWT token的工具类:
@Slf4j@ComponentpublicclassJwtTokenUtil{privatestaticfinalString CLAIM_KEY_USERNAME="sub";privatestaticfinalString CLAIM_KEY_CREATED="created";@Value("${jwt.secret}")privateString secret;@Value("${jwt.expiration}")privateLong expire;/**
* 从token中获取登录用户名
*/publicStringgetUserNameFromToken(String token){String username;try{Claims claims=getClaimsFromToken(token);
username= claims.getSubject();}catch(Exception e){
username=null;}return username;}/**
* 校验token
*/publicbooleanvalidateToken(String token,UserDetails userDetails){String username=getUserNameFromToken(token);return username.equals(userDetails.getUsername())&&!isTokenExpired(token);}/**
* 根据用户信息生成token
*/publicStringgenerateToken(UserDetails userDetails){Map<String,Object> claims=newHashMap<>();
claims.put(CLAIM_KEY_USERNAME, userDetails.getUsername());
claims.put(CLAIM_KEY_CREATED,newDate());returngenerateToken(claims);}/**
* 判断token是否已经失效
*/privatebooleanisTokenExpired(String token){Date expiredDate=getClaimsFromToken(token).getExpiration();return expiredDate.before(newDate());}privateStringgenerateToken(Map<String,Object> claims){returnJwts.builder().setClaims(claims).setExpiration(generateExpirationDate())//签名算法.signWith(SignatureAlgorithm.HS512, secret).compact();}/**
* 生成token的过期时间
*/privateDategenerateExpirationDate(){returnnewDate(System.currentTimeMillis()+ expire*1000);}privateClaimsgetClaimsFromToken(String token){Claims claims=null;try{
claims=Jwts.parser().setSigningKey(secret).parseClaimsJws(token).getBody();}catch(Exception e){
log.info("JWT格式验证失败:{}",token);}return claims;}}4. 添加SpringSecurity的配置类
spring security和spring mvc做了很好的集成,一共只需要做两件事,给web配置类加上@EanbleWebSecurity,继承WebSecurityConfigurerAdapter定义个性化配置。
这里我们在加上一个全局的注解@EnableGlobalMethodSecurity(prePostEnabled=true),该注解会在方法执行前进行验证。
configure(HttpSecurity httpSecurity):用于配置需要拦截的url路径、jwt过滤器及出异常后的处理器;
configure(AuthenticationManagerBuilder auth):用于配置UserDetailsService及PasswordEncoder;
UserDetailsService: SpringSecurity定义的核心接口,用于根据用户名获取用户信息,需要自行实现;
UserDetails:SpringSecurity定义用于封装用户信息的类(主要是用户信息和权限),需要自行实现;
PasswordEncoder:SpringSecurity定义的用于对密码进行编码及比对的接口,目前使用的是BCryptPasswordEncoder;
JwtAuthenticationTokenFilter:在用户名和密码校验前添加的过滤器,如果有jwt的token,会自行根据token信息进行登录。
@Configuration@EnableWebSecurity@EnableGlobalMethodSecurity(prePostEnabled=true)publicclassSpringSecurityConfigextendsWebSecurityConfigurerAdapter{@AutowiredprivateCustomAccessDeniedHandler customAccessDeniedHandler;@AutowiredprivateCustomAuthenticationEntryPoint customAuthenticationEntryPoint;@AutowiredprivateXlUserService xlUserService;@Overrideprotectedvoidconfigure(HttpSecurity httpSecurity)throwsException{
httpSecurity.csrf().disable()// 由于使用的是JWT,我们这里不需要csrf.sessionManagement()// 基于token,所以不需要session.sessionCreationPolicy(SessionCreationPolicy.STATELESS).and().authorizeRequests()// 允许对于网站静态资源的无授权访问.antMatchers(HttpMethod.GET,"/","/*.html","/favicon.ico","/**/*.html","/**/*.css","/**/*.js","/swagger-resources/**","/v2/api-docs/**").permitAll()// 对登录注册要允许匿名访问.antMatchers("/ucenter/xl-user/login","/ucenter/xl-user/register").permitAll()//跨域请求会先进行一次options请求.antMatchers(HttpMethod.OPTIONS).permitAll().anyRequest()// 除上面外的所有请求全部需要鉴权认证.authenticated();// 禁用缓存
httpSecurity.headers().cacheControl();// 添加JWT filter
httpSecurity.addFilterBefore(jwtAuthenticationTokenFilter(),UsernamePasswordAuthenticationFilter.class);//添加自定义未授权和未登录结果返回
httpSecurity.exceptionHandling().accessDeniedHandler(customAccessDeniedHandler).authenticationEntryPoint(customAuthenticationEntryPoint);}@Overrideprotectedvoidconfigure(AuthenticationManagerBuilder auth)throwsException{
auth.userDetailsService(userDetailsService()).passwordEncoder(passwordEncoder());}@Bean@OverridepublicUserDetailsServiceuserDetailsService(){//获取登录用户信息return username->{XlUser user= xlUserService.getUserByCode(username);if(user!=null){List<XlResource> permissionList= xlUserService.getResourceList(user.getUserId());returnnewJwtUser(user,permissionList);}thrownewUsernameNotFoundException("用户名或密码错误");};}/**
* 装载BCrypt密码编码器
*/@BeanpublicPasswordEncoderpasswordEncoder(){returnnewBCryptPasswordEncoder();}/**
* JWT filter
*/@BeanpublicJwtAuthenticationTokenFilterjwtAuthenticationTokenFilter(){returnnewJwtAuthenticationTokenFilter();}}5. 添加自定义结果处理类
5.1 添加CustomAccessDeniedHandler
当用户没有访问权限时的处理器,用于返回JSON格式的处理结果(若配置了全局异常的需要注意,会导致该处理类失效。需要在全局异常类里面在单独处理AccessDeniedException异常 );
@ComponentpublicclassCustomAccessDeniedHandlerimplementsAccessDeniedHandler{@Overridepublicvoidhandle(HttpServletRequest httpServletRequest,HttpServletResponse httpServletResponse,AccessDeniedException e)throwsIOException,ServletException{
httpServletResponse.setCharacterEncoding("UTF-8");
httpServletResponse.setContentType("application/json");
httpServletResponse.getWriter().println(JSONUtil.parse(R.error(ResultCodeEnum.FORBIDDEN.getCode(),ResultCodeEnum.FORBIDDEN.getMessage())));
httpServletResponse.getWriter().flush();}}5.2 添加CustomAuthenticationEntryPoint
当未登录或token失效时,返回JSON格式的结果。
@ComponentpublicclassCustomAuthenticationEntryPointimplementsAuthenticationEntryPoint{@Overridepublicvoidcommence(HttpServletRequest httpServletRequest,HttpServletResponse httpServletResponse,AuthenticationException e)throwsIOException,ServletException{
httpServletResponse.setCharacterEncoding("UTF-8");
httpServletResponse.setContentType("application/json");
httpServletResponse.getWriter().println(JSONUtil.parse(R.error(ResultCodeEnum.UNAUTHORIZED.getCode(),ResultCodeEnum.UNAUTHORIZED.getMessage())));
httpServletResponse.getWriter().flush();}}6. 添加JwtUser类
Spring Security需要我们实现几个东西,第一个是UserDetails:这个接口中规定了用户的几个必须要有的方法,所以我们创建一个JwtUser类来实现这个接口。为什么不直接使用User类?因为这个UserDetails完全是为了安全服务的,它和我们的领域类可能有部分属性重叠,但很多的接口其实是安全定制的,所以最好新建一个类:
publicclassJwtUserimplementsUserDetails{privateXlUser user;privateList<XlResource> resourceList;publicJwtUser(XlUser user,List<XlResource> resourceList){this.user= user;this.resourceList= resourceList;}@OverridepublicCollection<?extendsGrantedAuthority>getAuthorities(){//返回当前用户的权限return resourceList.stream().map(resource->newSimpleGrantedAuthority(resource.getResourceId()+":"+resource.getResourceName())).collect(Collectors.toList());}@OverridepublicStringgetPassword(){return user.getPassWord();}@OverridepublicStringgetUsername(){return user.getUserCode();}/**
* 账户是否未过期
**/@OverridepublicbooleanisAccountNonExpired(){returntrue;}/**
* 账户是否未锁定
**/@OverridepublicbooleanisAccountNonLocked(){returntrue;}/**
* 密码是否未过期
**/@OverridepublicbooleanisCredentialsNonExpired(){returntrue;}/**
* 账户是否激活
**/@OverridepublicbooleanisEnabled(){return user.getStatus().equals(1);}}7. 添加过滤器JwtAuthenticationTokenFilter
用户除登录之外的请求,都要求必须携带JWT Token。所以我们需要另外一个Filter对这些请求做一个拦截。这个拦截器主要是提取header中的token,进行校验。
@Slf4jpublicclassJwtAuthenticationTokenFilterextendsOncePerRequestFilter{@Value("${jwt.tokenHeader}")privateString tokenHeader;@Value("${jwt.tokenHead}")privateString tokenHead;@AutowiredprivateJwtTokenUtil jwtTokenUtil;@AutowiredprivateUserDetailsService userDetailsService;@OverrideprotectedvoiddoFilterInternal(HttpServletRequest httpServletRequest,HttpServletResponse httpServletResponse,FilterChain filterChain)throwsServletException,IOException{String authHeader= httpServletRequest.getHeader(this.tokenHeader);if(StringUtils.isNotBlank(authHeader)&& authHeader.startsWith(this.tokenHead)){String authToken= authHeader.substring(this.tokenHead.length());String username= jwtTokenUtil.getUserNameFromToken(authToken);
log.info("checking authentication "+ username);if(StringUtils.isNotBlank(username)&&SecurityContextHolder.getContext().getAuthentication()==null){UserDetails userDetails=this.userDetailsService.loadUserByUsername(username);// 校验tokenif(jwtTokenUtil.validateToken(authToken, userDetails)){UsernamePasswordAuthenticationToken authentication=newUsernamePasswordAuthenticationToken(
userDetails,null, userDetails.getAuthorities());
authentication.setDetails(newWebAuthenticationDetailsSource().buildDetails(
httpServletRequest));
log.info("authenticated user "+ username+", setting security context");SecurityContextHolder.getContext().setAuthentication(authentication);}}}
filterChain.doFilter(httpServletRequest, httpServletResponse);}}四、编写注册、登录方法
1. 编写controller
@Api(tags="后台用户管理")@RestController@RequestMapping("/ucenter/xl-user")publicclassXlUserController{@Autowiredprivate